SSH-MITM - ssh audits made simple
SSH-MITM is an open-source man-in-the-middle SSH server for security audits and malware analysis. It intercepts SSH sessions in real time — supporting password and public-key authentication, session hijacking, file transfer interception, and port forwarding — through a flexible plugin system.
Legal Notice
SSH-MITM is intended for authorized security audits, penetration testing, and research only. Do not use it against systems you do not own or have explicit written permission to test. Unauthorized interception of SSH traffic may be illegal in your jurisdiction. See the Legal Notice for details.
Features
Mirror live SSH sessions and interact with them in real time. Commands executed in either session appear in both.
Intercept, store, or replace files during SCP and SFTP transfers without interrupting the client.
Intercept TCP tunnels and dynamic port forwarding with full SOCKS 4/5 support.
Supports password and public-key authentication with automatic fallback. Redirect sessions without a forwarded agent to a honeypot.
Intercept hardware token authentication via the trivial authentication attack (CVE-2021-36367, CVE-2021-36368).
Learn SSH-MITM step by step in a browser-based guide — no target
server needed. Run ssh-mitm tutorial to get started.
Explore all available plugins and their configuration options interactively in the terminal — without editing any files.
Quick Start
Placed between a client and its SSH server, SSH-MITM intercepts the connection transparently — forwarding it to the target while giving the auditor full visibility and control:
1. Install
No installation required. Download the AppImage and you are ready to go:
$ wget https://github.com/ssh-mitm/ssh-mitm/releases/latest/download/ssh-mitm-x86_64.AppImage
$ chmod +x ssh-mitm-x86_64.AppImage
For other installation options (pip, Flatpak, Snap) see the installation guide.
2. Start SSH-MITM
Point SSH-MITM at your target host — use a system you are authorized to test:
$ ./ssh-mitm-x86_64.AppImage server --remote-host <target-host>
3. Route a client connection
Have the SSH client connect through SSH-MITM on port 10022:
$ ssh -p 10022 user@mitm-host
SSH-MITM intercepts the session and logs the credentials immediately:
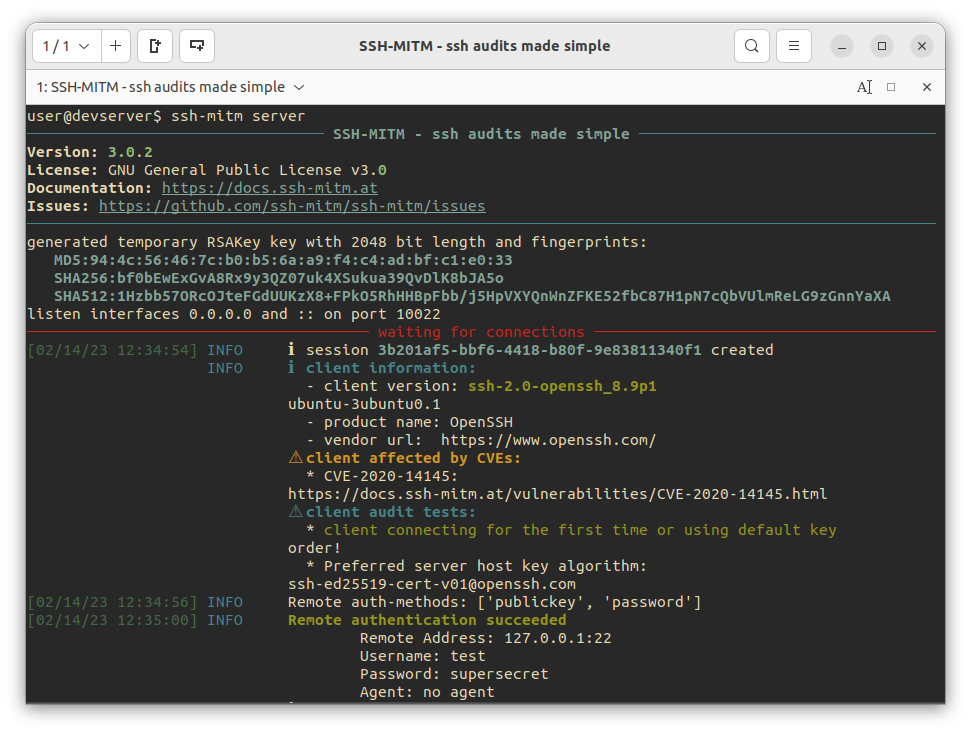
4. Attach to the live session
For every intercepted connection, SSH-MITM opens a mirror shell on a local port:
Connect to it from a separate terminal:
$ ssh -p 34463 127.0.0.1
The mirror shell reflects the session in real time. The auditor can observe the user’s activity and inject commands independently, without affecting the original connection.
